Secure Boot Certificate Expiration: Update Your PC to Stay Protected
- A silent but critical security update is rolling out for Windows PCs, addressing the impending expiration of Secure Boot certificates.
- Secure Boot, a feature built into the Unified Extensible Firmware Interface (UEFI), relies on a chain of trust.
- Microsoft estimates that almost a billion PCs currently in use could be affected.
A silent but critical security update is rolling out for Windows PCs, addressing the impending expiration of Secure Boot certificates. While most users won’t need to take action, the potential impact is significant: nearly a billion PCs running older versions of Windows are potentially vulnerable. The issue centers around certificates that verify the integrity of the boot process, ensuring that only trusted software loads during startup. These certificates, some dating back to , have a lifespan of approximately , and many will begin to expire in .
Secure Boot, a feature built into the Unified Extensible Firmware Interface (UEFI), relies on a chain of trust. This chain begins with a Key Exchange Key (KEK) embedded in the UEFI firmware, used by the Trusted Platform Module (TPM) to authorize the boot loader. The system then consults two databases: the Allowed Signature Database (DB) and the Forbidden Signature Database (DBX) to verify the authenticity of each component loaded during the boot sequence. Without valid certificates, this verification process breaks down, potentially allowing malicious software to compromise the system before the operating system even loads.
Microsoft estimates that almost a billion PCs currently in use could be affected. This includes any PC manufactured between and that hasn’t received a certificate update. The consequence isn’t a complete inability to boot, but a significant weakening of security. As Microsoft explains, the PC will still function, but critical protections against malware and unauthorized software installations will be diminished.
The good news is that Microsoft has been proactively addressing this issue. Starting in , the company collaborated with PC manufacturers to ensure that new systems shipped with updated certificates. For users with PCs purchased in the last year, no action is typically required. However, for those with older machines, an update is necessary.
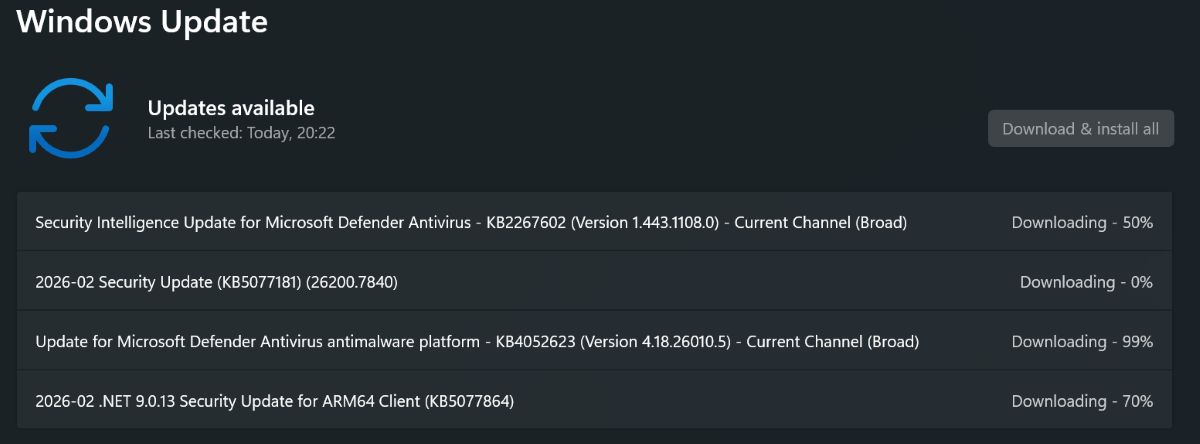
Fortunately, Microsoft is automating the certificate update process for systems that still receive Windows updates. This includes all versions of Windows 11 and Windows 10 that are within their extended support lifecycle. The February update package includes the necessary certificates, meaning that most users will be protected automatically.
Users can verify whether their system has the updated certificate by running a command in PowerShell with administrator privileges: ([System.Text.Encoding]::ASCII.GetString((Get-SecureBootUEFI db).bytes) -match 'Windows UEFI CA 2023'). A return value of “True” indicates that the system has a certificate issued in and is protected for the next . If the result is “False,” applying the February update is crucial.
Beyond Windows Update, Microsoft recommends checking the website of your PC manufacturer for dedicated update packages. This is particularly important for systems that may not receive updates directly through Windows Update or for specialized hardware configurations.
The timing of this update is somewhat ironic, given Microsoft’s recent efforts to restrict Windows 11 installations on older hardware. However, the company’s commitment to providing extended support, driven in part by regulatory pressure from the European Union, necessitates this broader security update. As Microsoft notes in a blog post, this effort extends support to nearly a billion PCs.
While the expiration of these certificates presents a potential security risk, the situation is manageable. Even if you don’t update immediately, there’s still time before . However, proactively applying the update is the most prudent course of action. In the worst-case scenario, an unpatched system remains vulnerable, but still functional. Applying the new certificates now provides peace of mind and ensures the continued integrity of your system’s boot process. As a personal anecdote, I recently dusted off an older Toshiba laptop running Windows 10 and have been running updates for the past three hours, hoping to resolve both the operating system version and the UEFI certificate. A little preventative maintenance can go a long way.
More information is available from Microsoft here.
