7 Keys to Understanding DDoS-for-Hire Attacks
The Rise of DDoS-for-Hire: A Growing Threat to U.S. businesses
The landscape of cyberattacks is evolving, with DDoS-for-hire services becoming increasingly elegant and accessible. This new breed of cyber threat demands a fresh approach to cybersecurity for U.S. businesses.
Gone are the days when launching a Distributed Denial of Service (DDoS) attack required technical expertise. Today, anyone with an internet connection and a few dollars can rent a botnet and unleash a crippling cyberattack. This alarming trend is fueled by the rise of DDoS-for-hire services, platforms that offer easy-to-use tools and automated attacks, making them accessible to a wider range of malicious actors.
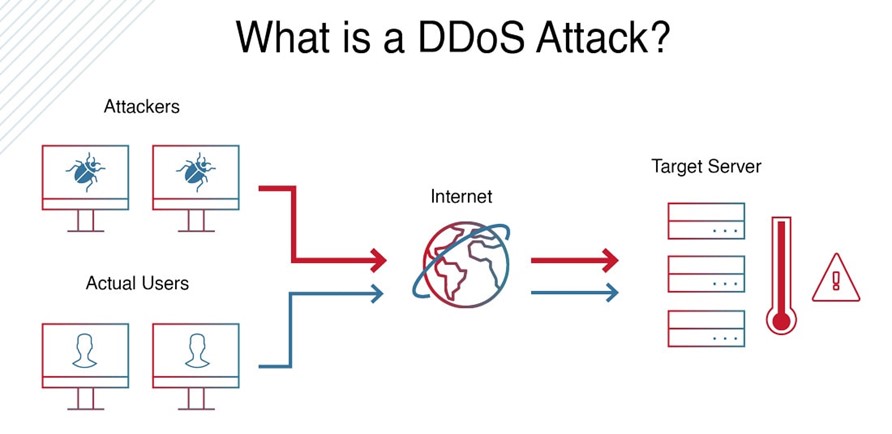
These services operate by allowing users to rent networks of compromised devices, known as botnets, to flood target servers with traffic, overwhelming their capacity and causing service disruptions.While marketed as legitimate tools for network stress testing, they are often misused to target critical infrastructure, businesses, and even individuals.
The accessibility of these platforms is a major contributing factor to their proliferation. Promoted on clandestine forums, social media, and even open-source platforms like GitHub, these services often bypass traditional barriers to entry, such as account creation or email verification. This ease of access has broadened their appeal, attracting not only seasoned cybercriminals but also hacktivists and opportunistic individuals.
adding to the danger, DDoS-for-hire services are no longer limited to basic tools. They now offer advanced features, including reconnaissance tools to identify network vulnerabilities, API integrations for customization, and scheduling and automation capabilities for complex, multi-stage attacks. These innovations,once exclusive to highly skilled attackers,are now readily available to anyone,significantly amplifying the threat to organizations.
This evolution has been notably pronounced in the last three years, with automation becoming a defining characteristic. Attackers can now program repeated, optimized attacks, eliminating the need for manual intervention. This professionalization of DDoS-for-hire services has dramatically increased their destructive potential, allowing them to target entire networks with devastating consequences.
for U.S. businesses, the rise of DDoS-for-hire services presents a serious and growing threat.These attacks, with their integrated tools and automation capabilities, can quickly identify and exploit vulnerabilities, rendering traditional defenses ineffective. Their ability to adapt in real-time allows them to bypass conventional mitigation techniques, such as bandwidth throttling.
The consequences of a successful DDoS attack can be severe, including financial losses, operational disruptions, and damage to customer trust.U.S. businesses must recognize the urgency of this threat and adopt proactive defense strategies. Leveraging artificial intelligence and real-time analysis is crucial for effectively detecting and mitigating these increasingly sophisticated attacks.
DDoS-for-Hire: A Chat with Cybersecurity Expert Dr. Emily Carter
ND3: The landscape of cyberattacks is evolving rapidly, and DDoS-for-hire services pose a significant threat. Dr. Emily Carter, a leading cybersecurity expert, joins us today to shed light on this alarming trend. Dr.Carter,thanks for being with us.
Dr. Carter: My pleasure. It’s vital to raise awareness about this growing threat.
ND3: Let’s start with the basics. What exactly are DDoS-for-hire services?
dr. Carter: Essentially, these are platforms that allow anyone to rent a network of compromised computers, known as a botnet, to launch denial-of-service attacks.These attacks overwhelm a target server with traffic, making it unavailable to legitimate users.
ND3: You mentioned that these services are becoming more accessible. What makes them so easy to use?
Dr. Carter: In the past, launching DDoS attacks required technical expertise.Now, DDoS-for-hire platforms offer user-friendly interfaces and even boast features like automated attacks and scheduling. You don’t need to be a hacker to weaponize these tools.
ND3: What kind of damage can these attacks inflict on U.S. businesses?
Dr. Carter: The consequences can be devastating. Downed websites,disrupted operations,financial losses,and damaged reputation are just some of the potential impacts.For businesses that rely heavily on online operations, a prosperous DDoS attack can be crippling.
ND3: How are businesses expected to defend against this new breed of attack?
Dr.Carter: conventional security measures are often insufficient. Businesses need to adopt a multi-layered approach that includes proactive threat intelligence, robust network security infrastructure, and advanced ddos mitigation solutions.
ND3: Are there any emerging technologies that can definitely help combat this threat?
Dr.Carter: Artificial intelligence and machine learning are showing great promise for detecting and mitigating DDoS attacks in real-time. These technologies can analyze network traffic patterns and identify anomalies that indicate an attack is underway.
ND3: Any final words of advice for our readers?
Dr. Carter: DDoS-for-hire services are a serious and growing threat. Businesses need to be aware of the risks and take proactive steps to strengthen their defenses. It’s not a matter of “if” but “when” they will be targeted.
