Hackers Use Mac Script Editor to Install Malware
- Cybersecurity researchers have identified a new method used by attackers to deliver malware to macOS users by leveraging Script Editor, a native Apple application.
- Historically, ClickFix attacks on macOS attempted to trick victims into copying and pasting malicious commands directly into the Terminal application.
- To circumvent the protections in macOS 26.4, attackers have shifted their focus to Script Editor.
Cybersecurity researchers have identified a new method used by attackers to deliver malware to macOS users by leveraging Script Editor, a native Apple application. This technique is being used to bypass recent security enhancements introduced by Apple to prevent the execution of malicious commands.
The attack is part of a broader campaign known as ClickFix. Historically, ClickFix attacks on macOS attempted to trick victims into copying and pasting malicious commands directly into the Terminal application. However, with the release of macOS Tahoe 26.4, Apple implemented a security feature that scans all pasted commands before they are executed, effectively neutralizing that specific infection vector.
The Shift to Script Editor
To circumvent the protections in macOS 26.4, attackers have shifted their focus to Script Editor. This built-in macOS tool allows users to write, edit and run scripts using AppleScript and JavaScript to automate tasks and control other applications.
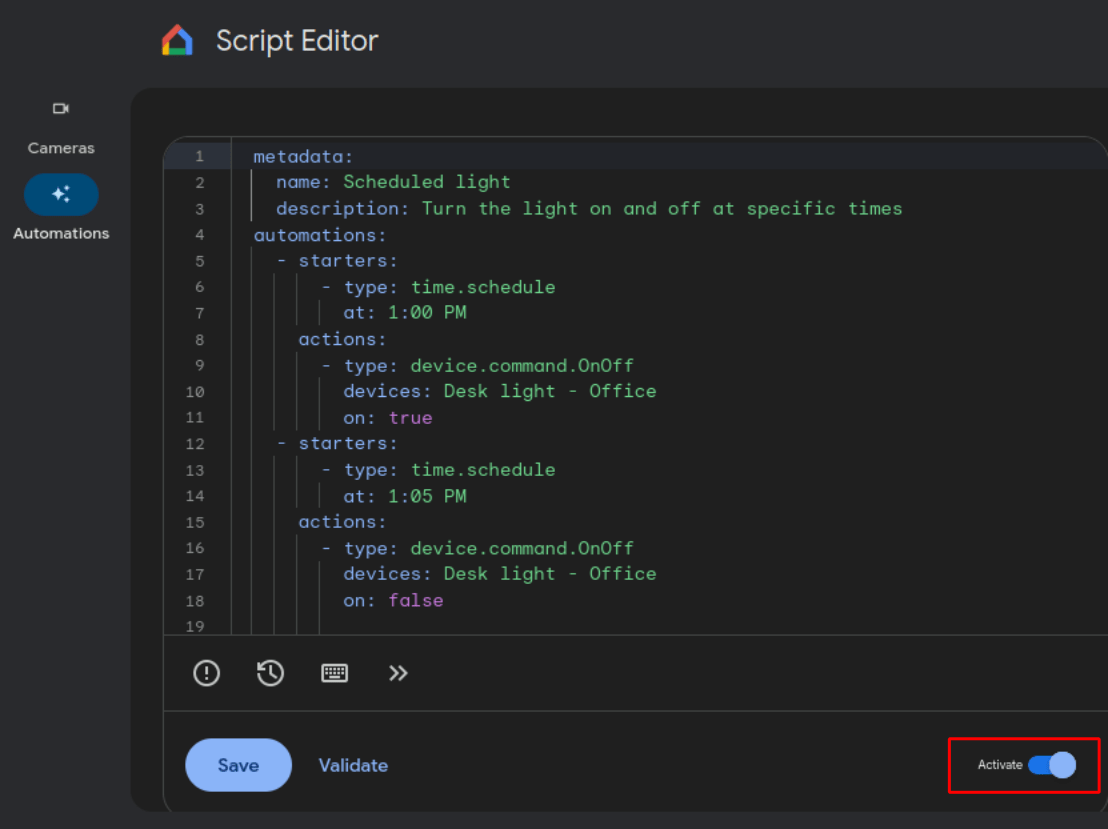
According to Jamf Threat Labs, attackers are now using a URL scheme to trigger the launch of Script Editor on a victim’s device. Once the application is open, it serves as an entry point for the delivery of Atomic Stealer, a piece of infostealer malware designed to exfiltrate sensitive data from the infected system.
In some instances, the malware is delivered through fake disk storage warnings. In other cases, the attack leverages compiled AppleScript files with the .scpt extension. These files open directly in Script Editor, which provides a legitimate-looking interface that can deceive users into thinking they are performing a standard system operation.
Social Engineering and Gatekeeper Bypass
The attack relies heavily on social engineering to convince users to execute the malicious code. Attackers frequently disguise the malware as legitimate software updates for popular applications, including Microsoft Teams, Zoom, and Google Chrome.
When a user double-clicks a malicious .scpt file, they are presented with an interface that appears benign, often framed as part of an installation or update process. The users are then prompted to click Run
or press Command + R to complete the process, which unintentionally executes the embedded malicious payload.
This method is particularly effective because it can bypass Apple’s Gatekeeper security mechanisms. While Gatekeeper may quarantine these files, researchers found that users can still manually execute them within Script Editor, effectively overriding the built-in protections.
Evolution of macOS Malware Vectors
The transition to using .scpt files follows a pattern of adaptation by cybercriminals. In 2024, Apple removed the right-click and open Gatekeeper override, which had been a widely abused infection vector. Since that removal, attackers have increasingly turned to native scripting tools to hide their payloads in plain sight.
The use of Script Editor is significant because it is a trusted, signed Apple application. By routing the attack through a legitimate system tool, the malware avoids triggering the same alarms that would occur if a user attempted to run an unsigned third-party binary.
- Delivery Method: Use of URL schemes and .scpt files to launch Script Editor.
- Deception Tactics: Fake software updates for Zoom, Teams, and Chrome, or fake disk storage warnings.
- Payload: Atomic Stealer malware used for data exfiltration.
- Bypass Target: macOS Tahoe 26.4 command scanning and Gatekeeper quarantine.
The emergence of this vector highlights a persistent trend where attackers weaponize native administrative tools to evade evolving operating system security layers.
