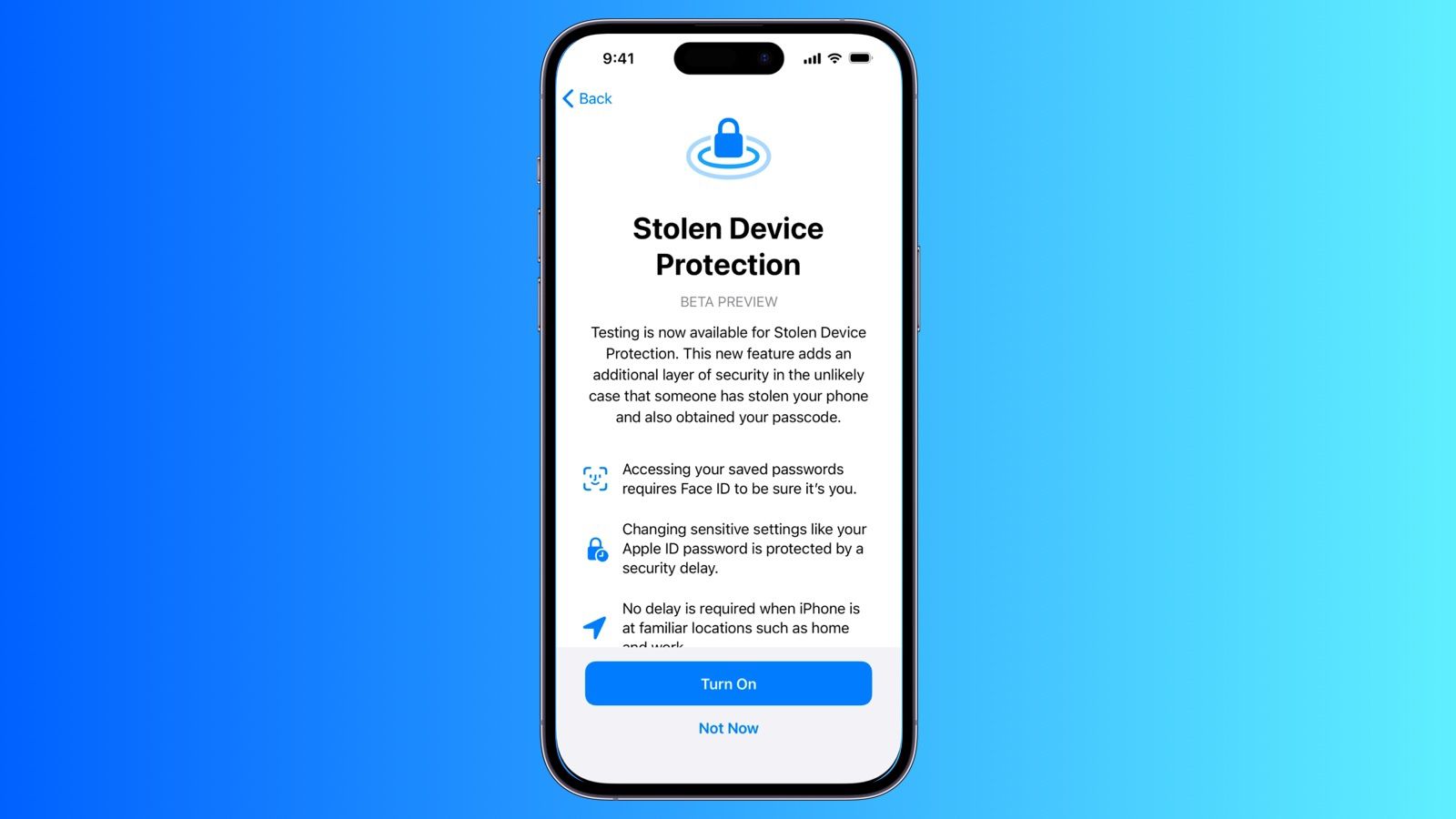
iOS 26.4: Stolen Device Protection Now Enabled by Default for iPhones
- Apple is bolstering iPhone security with a significant update to its Stolen Device Protection feature, now enabled by default for all users with the release of iOS 26.4.
- The original threat, as Apple discovered, involved thieves surveilling victims to learn their passcodes.
- At its core, Stolen Device Protection requires additional verification through Face ID or Touch ID for a range of critical actions.
Apple is bolstering iPhone security with a significant update to its Stolen Device Protection feature, now enabled by default for all users with the release of iOS 26.4. Introduced initially in 2023 to combat a sophisticated theft method, the feature adds layers of authentication to prevent unauthorized access to sensitive data even if a thief knows the device’s passcode.
The original threat, as Apple discovered, involved thieves surveilling victims to learn their passcodes. Once obtained, criminals could bypass security measures, emptying bank accounts, accessing passwords stored in iCloud Keychain, and disabling Find My functionality – effectively rendering the stolen device untraceable and enabling widespread financial and personal data theft. Stolen Device Protection directly addresses this vulnerability.
At its core, Stolen Device Protection requires additional verification through Face ID or Touch ID for a range of critical actions. This goes beyond simply entering the passcode. Specifically, users will now need biometric authentication to view or use passwords and passkeys saved in iCloud Keychain, apply for a new Apple Card, view an Apple Card virtual card, turn off Lost Mode, erase all content and settings, conduct certain Apple Cash and Savings transactions, use saved payment methods in Safari, or even use their iPhone to set up a new device. Crucially, none of these actions offer a passcode fallback; biometric authentication is mandatory.
Beyond these immediate actions, a second tier of security applies to changes that could fundamentally compromise an account. Changing an Apple ID password, updating account security settings (adding or removing trusted devices, phone numbers, Recovery Keys, or Recovery Contacts), changing the iPhone passcode itself, adding or removing Face ID or Touch ID, turning off Find My, and even disabling Stolen Device Protection are all subject to a one-hour security delay *and* require two successful biometric authentications. This delay provides a critical window for the legitimate owner to mark the device as lost and secure their account.
Prior to iOS 26.4, users had to manually enable Stolen Device Protection within the Face ID and Passcode settings. The update streamlines security by activating it for everyone. Apple also allows users to configure the feature to always require these additional security measures, even when the iPhone is in a familiar location – such as a home or workplace – offering a heightened level of protection for particularly security-conscious individuals. The system intelligently recognizes familiar locations, minimizing disruption for everyday use while maintaining robust security when the device is away from these trusted areas.
The implementation of a security delay is a key component of the system’s effectiveness. It’s designed to thwart quick, opportunistic changes made by a thief who has obtained both the passcode and physical possession of the device. The one-hour delay, coupled with the requirement for biometric authentication, significantly increases the difficulty of exploiting stolen iPhones.
While iOS 26.4 is currently available to developers, a public beta is expected to follow shortly, with a general release planned for the spring. This phased rollout allows Apple to gather feedback and refine the feature before it reaches the broader user base.
The move to enable Stolen Device Protection by default represents a significant step forward in mobile security. By proactively addressing a specific and evolving threat, Apple is raising the bar for device protection and providing users with a more secure experience. The reliance on biometric authentication, coupled with the security delay, creates a robust defense against unauthorized access and data breaches, even in the event of physical theft. The feature’s design balances security with usability, minimizing disruption for legitimate users while maximizing protection against malicious actors.
