Kimwolf Botnet Disrupts I2P Network with Sybil Attack
- The Invisible Internet Project (I2P), a network designed for anonymous and secure communication, has been facing significant disruptions over the past week due to an influx of traffic...
- Kimwolf surfaced in late 2025, rapidly infecting millions of poorly secured Internet of Things (IoT) devices – including TV streaming boxes, digital picture frames, and routers – and...
- I2P operates as a decentralized, privacy-focused network, routing data through multiple encrypted layers across volunteer-operated nodes.
The Invisible Internet Project (I2P), a network designed for anonymous and secure communication, has been facing significant disruptions over the past week due to an influx of traffic originating from the Kimwolf botnet. While Kimwolf is primarily known for its distributed denial-of-service (DDoS) capabilities, its recent activity represents a novel tactic: leveraging I2P’s infrastructure to bolster its own resilience against takedown attempts.
Kimwolf surfaced in late 2025, rapidly infecting millions of poorly secured Internet of Things (IoT) devices – including TV streaming boxes, digital picture frames, and routers – and repurposing them as relays for malicious traffic. This botnet gained notoriety for launching abnormally large DDoS attacks, as documented in previous reports. The shift towards utilizing I2P marks a strategic evolution in its operational methods.
I2P operates as a decentralized, privacy-focused network, routing data through multiple encrypted layers across volunteer-operated nodes. This architecture is designed to conceal the locations of both the sender and receiver, providing a secure and censorship-resistant platform for private websites, messaging, and data sharing. As the I2P website explains, the network’s strength lies in its distributed nature and encryption.
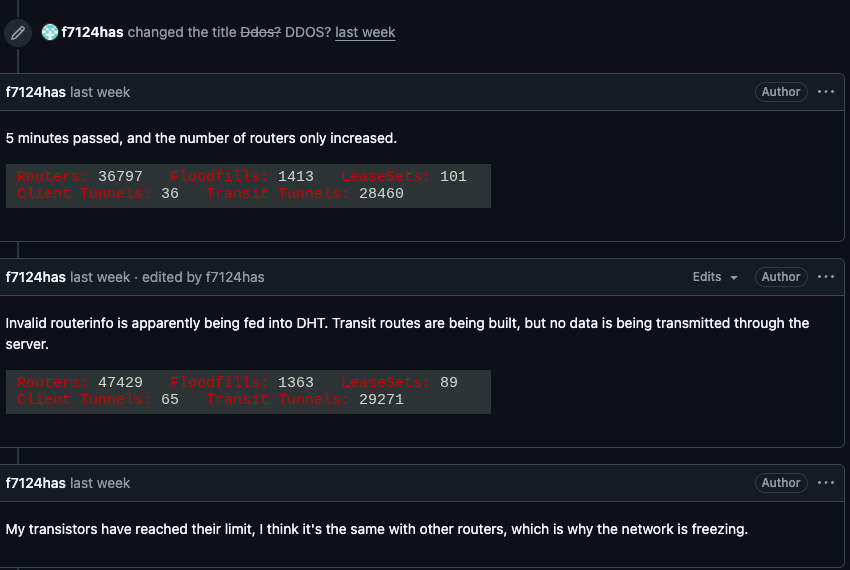
The disruptions began on , when I2P users reported tens of thousands of new routers suddenly joining the network. These routers were unable to transmit data, and their sheer volume overwhelmed the system, preventing legitimate users from connecting. A user on the I2P GitHub page reported their physical router freezing when the number of connections exceeded 60,000.
The source of the problem was quickly identified. According to a post on their Discord channel, the operators of Kimwolf inadvertently triggered the outages while attempting to integrate approximately 700,000 compromised bots as nodes within the I2P network. This incident highlights a “Sybil attack,” where a single entity attempts to gain disproportionate control over a peer-to-peer network by creating numerous fake identities.
The scale of the attempted integration is particularly noteworthy. While I2P’s Wikipedia page previously estimated the network consisted of around 55,000 computers globally, Lance James, founder of the cybersecurity consultancy Unit 221B and the original founder of I2P, now estimates the active network size to be between 15,000 and 20,000 devices on any given day. The Kimwolf botnet’s attempt to add hundreds of thousands of nodes far exceeded the network’s capacity.
Benjamin Brundage, founder of Synthient, a company specializing in tracking proxy services, explained that the Kimwolf operators are actively seeking to establish a command and control (C2) network that is resistant to takedown efforts. He noted that they have been experimenting with both I2P and Tor, another anonymity network, as potential backup C2 channels, though no widespread disruptions have been reported on Tor recently.
“I don’t think their goal is to take I2P down,” Brundage said. “It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts.”
Kimwolf’s activities have previously caused issues for other internet infrastructure providers. Late last year, the botnet instructed millions of infected devices to use Cloudflare’s Domain Name System (DNS) settings, resulting in Kimwolf’s control domains temporarily surpassing major websites like Amazon, Apple, Google, and Microsoft in Cloudflare’s public ranking of most requested domains.
Currently, I2P is operating at roughly half of its normal capacity. However, developers are releasing updates aimed at improving network stability over the coming week. Despite the disruption, the network remains operational.
Interestingly, Brundage also reported a recent development within the Kimwolf operation. He indicated that the botnet’s operators have alienated some of their more skilled developers and operators, leading to a significant reduction in the botnet’s size – a drop of over 600,000 infected systems – due to what appears to be a “rookie mistake.”
“It seems like they’re just testing stuff, like running experiments in production,” Brundage observed. “But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing.” This internal turmoil may offer a temporary reprieve from Kimwolf’s disruptive activities, but the incident underscores the ongoing challenges of combating sophisticated botnets and their evolving tactics.
