Kimwolf Botnet: Millions of Devices Infected Via Router & Android TV Vulnerabilities
- The security landscape for home networks has taken a concerning turn with the explosive growth of the Kimwolf botnet, an Android-based malware that’s quietly infecting over two million...
- Researchers first began tracking Kimwolf in late 2024, quickly realizing its potential for widespread disruption.
- A key element of Kimwolf’s success is its exploitation of residential proxy networks.
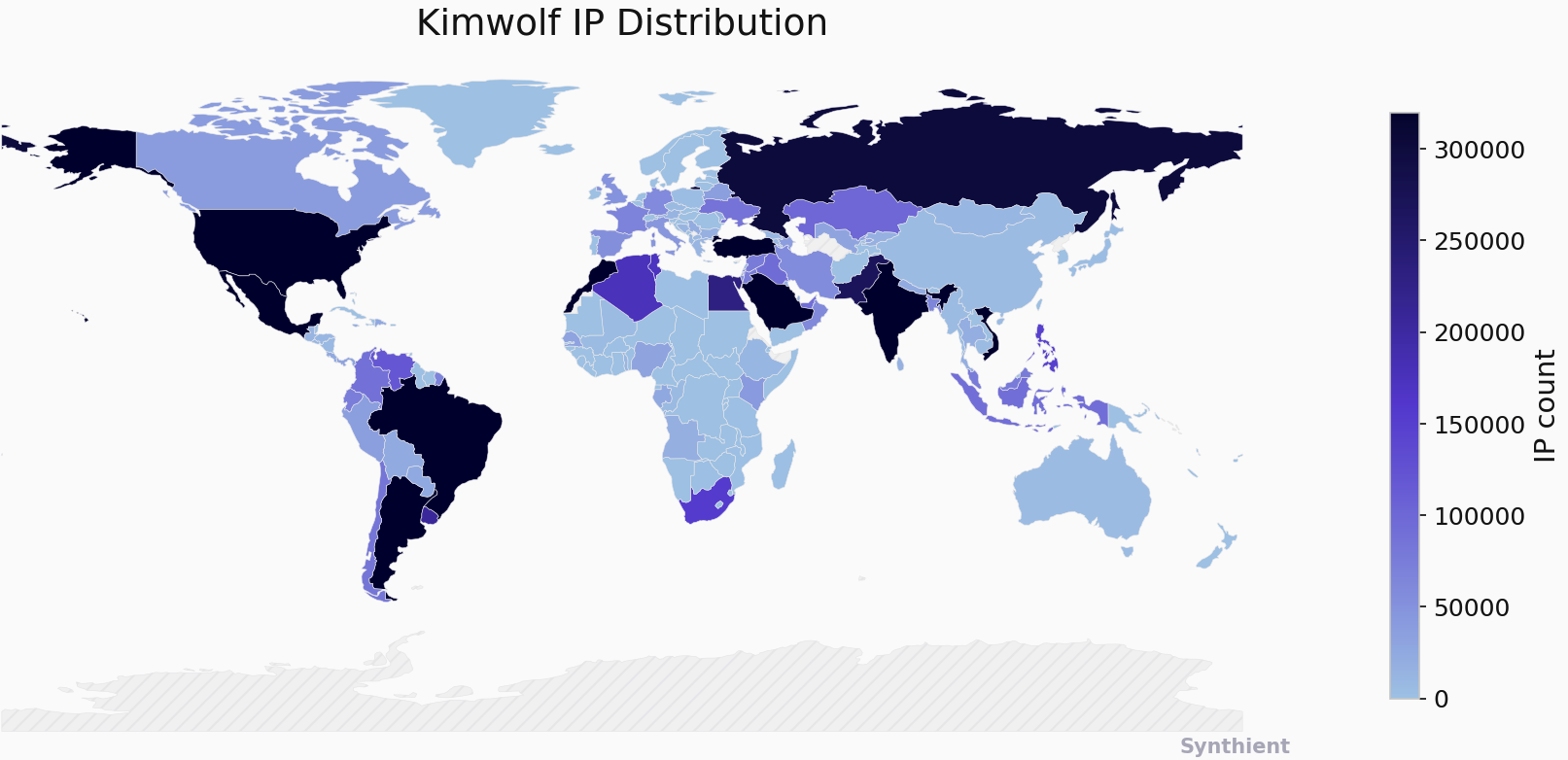
The security landscape for home networks has taken a concerning turn with the explosive growth of the Kimwolf botnet, an Android-based malware that’s quietly infecting over two million devices globally. What sets Kimwolf apart isn’t just its size, but its insidious method of spreading: exploiting vulnerabilities in residential proxy networks to burrow into the internal networks behind users’ firewalls, and routers.
Researchers first began tracking Kimwolf in late 2024, quickly realizing its potential for widespread disruption. The malware forces compromised systems to participate in malicious activities ranging from ad fraud and account takeovers to crippling distributed denial-of-service (DDoS) attacks. But the real danger lies in how easily it gains access – often through seemingly innocuous devices like Android TV boxes and digital photo frames.
A key element of Kimwolf’s success is its exploitation of residential proxy networks. These networks, marketed as a way to anonymize and localize web traffic, allow customers to route their internet connection through devices in various locations. However, Kimwolf leverages a weakness in these services, tunneling back through them to reach devices on internal networks. This allows the botnet to infect devices hidden behind what users believe is the protection of their home network.
The problem is particularly acute with unofficial Android TV boxes, often sold at low prices on major e-commerce platforms. Many of these devices ship with Android Debug Bridge (ADB) mode enabled by default, a diagnostic tool intended for manufacturing and testing. Leaving ADB enabled creates a significant security risk, allowing attackers to remotely configure and even update the device without authentication. According to Synthient, two-thirds of Kimwolf infections are found on these insecure Android TV boxes.
Benjamin Brundage, founder of the security firm Synthient, played a crucial role in uncovering the extent of Kimwolf’s reach. Brundage discovered that Kimwolf was exploiting a vulnerability allowing it to bypass restrictions on accessing internal network addresses. By manipulating Domain Name System (DNS) settings, the botnet could effectively tunnel into local networks, scanning for vulnerable devices.
Brundage’s research led him to identify IPIDEA, a China-based residential proxy network, as a major conduit for Kimwolf infections. He found a direct correlation between new Kimwolf infections and IP addresses offered for rent by IPIDEA, indicating the botnet was actively exploiting the network’s vulnerabilities. IPIDEA, which advertises access to over 100 million residential proxy endpoints, became a prime target for Kimwolf’s expansion.
After being alerted to the issue, IPIDEA implemented security changes to block access to internal network addresses and restrict traffic on high-risk ports. The company stated it had addressed a legacy module that allowed unauthorized access and was actively blocking malicious activity. However, the ease with which Kimwolf initially exploited the network highlights the risks associated with relying on residential proxy services without robust security measures.
The story of Kimwolf also echoes past incidents involving the 911S5 Proxy service, a similar residential proxy network that operated between 2014 and 2022. Like Kimwolf, 911S5 was exploited by cybercriminals for malicious purposes, ultimately leading to its shutdown and the sanctioning of its creators by the U.S. Treasury Department. The recurrence of these incidents underscores the need for greater scrutiny and security within the residential proxy industry.
The implications for users are significant. A compromised device on a home network can potentially expose other devices to attack, allowing attackers to modify router settings, intercept traffic, or install additional malware. The risk is amplified by the fact that many users are unaware of the vulnerabilities present in their devices or the potential for exploitation.
To mitigate the risk, experts recommend sticking to reputable brands when purchasing internet-connected devices and avoiding unofficial or suspiciously cheap alternatives. Enabling a guest network on your router can also help isolate potentially compromised devices from the rest of your home network. Synthient has also provided a tool on its website to check if your public IP address has been associated with Kimwolf activity.
The Kimwolf botnet serves as a stark reminder that the security of home networks is increasingly under threat. As attackers continue to develop new and innovative methods of exploitation, it’s crucial for users to remain vigilant and take proactive steps to protect their devices and data. The ease with which Kimwolf spread, and the vulnerabilities it exploited, demand a more robust approach to security across the entire ecosystem of internet-connected devices and proxy services.
