Online Scams: How to Protect Yourself in 2024
Protect Yourself From Rising Scams Targeting Multi-Factor Authentication and Email Attachments
Table of Contents
In today’s digital landscape, staying safe online requires constant vigilance. Scammers are continually evolving thier tactics, and two areas seeing a surge in malicious activity are multi-factor authentication (MFA) and email attachments. This article details how to recognize and avoid these increasingly refined threats, protecting yoru personal data and accounts.
Understanding multi-Factor Authentication (MFA) and Why It’s a Target
Multi-factor authentication, frequently enough called two-step verification, adds an extra layer of security to your online accounts. it works by requiring a code from an app on your phone, or a “yes/no” prompt, in addition to your password. While MFA is a powerful security tool, it’s now becoming a prime target for scammers.
“Multi-factor authentication attacks have been happening for well over a decade,” explains cybersecurity expert [Name – if available from source material, otherwise remove], “They just frequently take on new forms, or target new platforms such as the authenticator app.”
The latest scam revolves around “MFA fatigue,” a tactic designed to wear down your defenses.
The MFA “Fatigue” Scam: How it effectively works
This scam involves receiving a barrage of authentication requests through your MFA app, even when you haven’t initiated a login. The goal is to desensitize you to the notifications, hoping you’ll eventually approve a request without thinking, inadvertently granting a scammer access to your account.
“This scam is all about wearing you down to the point of clicking an unknown notification and accidentally providing your personal information,” warns [Name – if available from source material, otherwise remove].
Recognizing the Red Flags:
Unexpected Verification Requests: Your authentication app is requesting verification or providing a code you didn’t ask for.
Multiple, Unprompted Notifications: the app sends several notifications in a row, even though you didn’t attempt to log in anywhere.
What to Do if you’re Targeted:
If you experience a string of authentication app notifications,do not click approve. Approving a login you didn’t request is akin to handing your account keys to a stranger.
“You just don’t do it,” emphasizes [Name – if available from source material, otherwise remove].
Choosing a Secure Authentication App:
Not all MFA apps are created equal. Opt for apps that generate verification codes rather than relying solely on “push” notifications. Recommended options include:
2FAS
Aegis Authenticator
Microsoft Authenticator
Stratum
Google Authenticator
Push notifications are more vulnerable to this type of scam, as they pressure you into a quick decision.
Proactive Security Measures:
Beyond choosing a secure app,regularly changing your passwords is crucial. This limits the lifespan of stolen credentials that may be sold on the dark web.
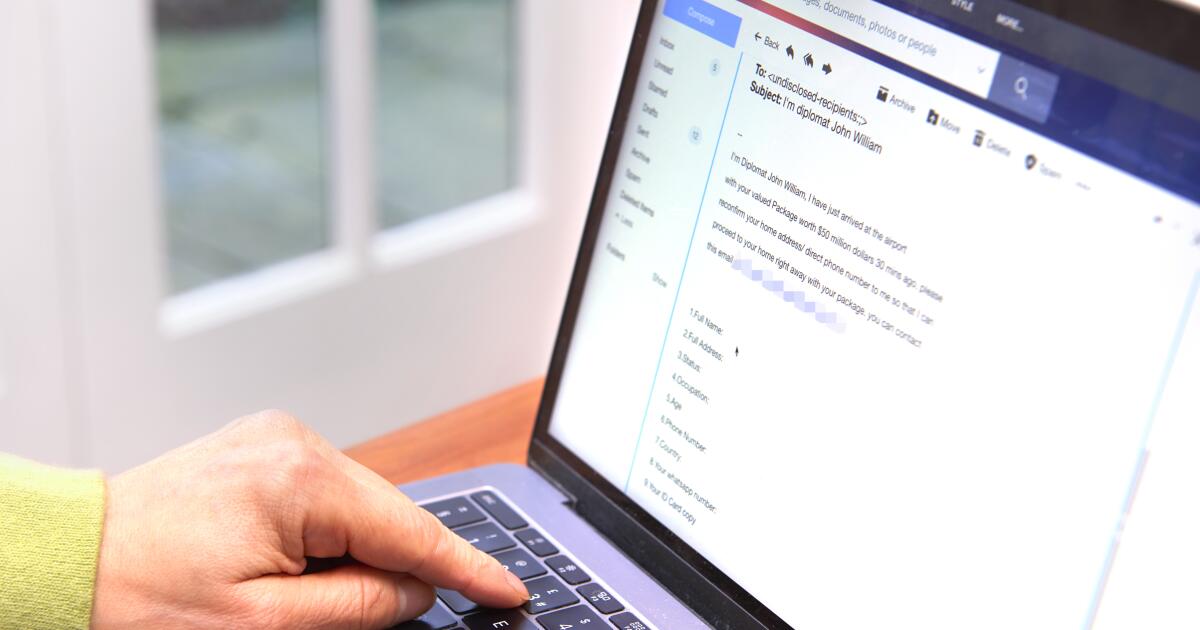
Beware of Emails with Suspicious HTML Attachments
Another common, yet persistent, scam involves emails containing unsolicited HTML attachments. These attachments can redirect you to phishing websites designed to steal your login credentials or download malware onto your device.
“It’s the oldest technique in the book but it’s still commonly used today,” says [Name – if available from source material, otherwise remove].
HTML files contain code that can execute malicious scripts, such as Javascript, which can install information-stealing malware or launch phishing pages. Scammers often impersonate trusted organizations to increase the likelihood of success.
“If an email is unsolicited,the end user should always question the identity of the emails being sent,” advises [name – if available from source material,or else remove].
Spotting a Suspicious Email:
Unknown Sender: The email originates from a contact you don’t recognize.
Unexpected Attachment: The attachment is unsolicited and appears suspicious.
Protecting Yourself from Email-Based Threats:
Always exercise extreme caution before opening any email attachment.
Look for typosquatting: Carefully examine the URL within the attachment (if previewed). Typosquatting occurs when scammers create domain names that are slight variations of legitimate websites (e.g., googel.com instead of google.com). These subtle differences can be easily overlooked, leading you to a malicious site.
Additional Security Tips:
Enable email filtering: Utilize your email provider’s spam and phishing filters.
Keep software updated: Regularly update your operating system, browser, and antivirus software.
**Report suspicious emails
