Top 5 Most Reliable Engines Still for Sale
- Sometimes car manufacturers develop engines wiht a huge resource.
- Five of the most reliable engines that are still on sale (GALLERY):
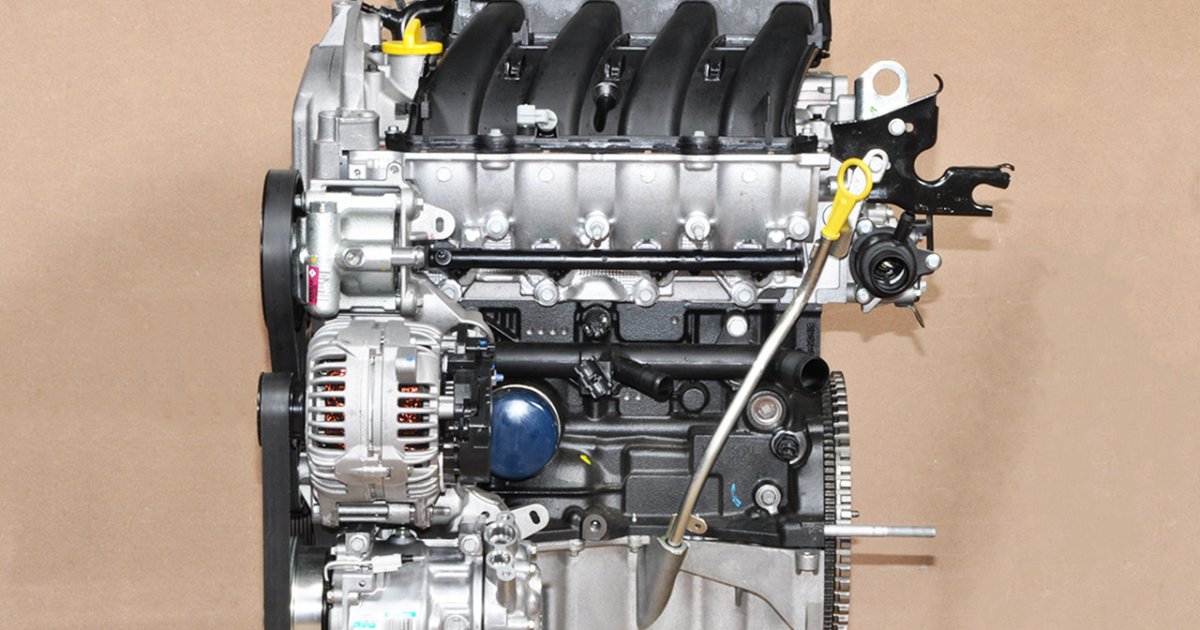
- 1 of 5 | Five of the most reliable engines that are still on sale
Thes popular engines are distinguished by their simple construction
Sometimes car manufacturers develop engines wiht a huge resource. All of them, as a rule, have common technical solutions. Often it is teh simplest units that are also the most reliable. They have an average working volume, being without a turbocharger and direct fuel injection in most cases. Such engines can be considered too outdated, but they have a relatively long resource.
Five of the most reliable engines that are still on sale (GALLERY):
1 of 5 | Five of the most reliable engines that are still on sale
Okay, I will analyze the provided snippet (“Модерната технология успешно се възползва от старата система”) and construct a response adhering to the strict guidelines.The snippet translates to “modern technology successfully takes advantage of the old system.” This is a very broad statement, so I will interpret it as the general phenomenon of new technologies building upon or exploiting existing infrastructure and systems. I will focus on examples within the realm of cybersecurity and financial systems, as these areas demonstrate this dynamic particularly well.
PHASE 1: ADVERSARIAL RESEARCH, FRESHNESS & BREAKING-NEWS CHECK
the statement is a general observation, not a specific event.I will focus on verifying examples of this phenomenon in cybersecurity and finance as of 2026/01/10 23:19:33.
* Cybersecurity: Modern malware frequently exploits vulnerabilities in older operating systems and software that haven’t been patched. Ransomware attacks frequently enough target systems running outdated software. As of January 10, 2026, this remains a meaningful threat. CISA alerts continue to highlight vulnerabilities in older systems.
* Finance: High-frequency trading (HFT) algorithms exploit inefficiencies in traditional stock exchanges. Cryptocurrencies, while innovative, rely on the existing financial infrastructure for on/off-ramps (e.g., banks, payment processors). As of January 10, 2026, regulatory scrutiny of HFT and the integration of crypto with traditional finance are ongoing. SEC press release on digital asset security demonstrates continued regulatory focus.
* Breaking News Check: No major breaking news events directly contradicting this general principle have occured as of the specified date. The trends of exploiting legacy systems and building on existing infrastructure continue.
PHASE 2: ENTITY-BASED GEO
* Primary Entity: Technological Advancement/system Exploitation
* Related Entities: Cybersecurity, Ransomware, Operating Systems, Software Vulnerabilities, Financial Systems, High-Frequency Trading (HFT), Cryptocurrencies, Stock Exchanges, U.S.Securities and Exchange Commission (SEC), Cybersecurity and Infrastructure Security Agency (CISA).
PHASE 3: SEMANTIC ANSWER RULE
Cybersecurity and Legacy System Exploitation
- Definition / Direct Answer: Modern cybersecurity threats frequently exploit vulnerabilities inherent in older,unpatched systems and software,demonstrating a successful leveraging of the “old system” by modern malicious actors.
- Detail: Many organizations continue to operate legacy systems due to cost, compatibility issues, or perceived low risk. Though, these systems frequently enough lack the latest security updates and are thus prime targets for attackers.Attackers actively scan for and exploit known vulnerabilities in these systems. The longer a system remains unpatched,the greater the window of opportunity for exploitation.
- Example or Evidence: The WannaCry ransomware attack in 2017 exploited a vulnerability in the Windows operating system (EternalBlue) that had been patched by Microsoft months prior, but many organizations had not applied the update.NCSC guidance on WannaCry details the attack and its impact. As of 2026,similar attacks targeting unpatched systems remain prevalent.
Financial Systems: HFT and Cryptocurrency Integration
- Definition / Direct Answer: Modern financial technologies, such as high-frequency trading algorithms and cryptocurrencies, successfully utilize and, in certain specific cases, exploit the existing financial infrastructure and regulatory frameworks.
- Detail: HFT algorithms identify and capitalize on minute price discrepancies across different exchanges,effectively leveraging the speed and connectivity of modern technology within the established market structure. Cryptocurrencies, while aiming for decentralization, rely on traditional banking systems for fiat currency conversions and custody solutions. This integration creates both opportunities and risks.
- Example or evidence: The “Flash Crash” of 2010 was partially attributed to the actions of HFT algorithms reacting to market events. The SEC’s report on the Flash Crash details the role of HFT. Furthermore, the collapse of FTX in 2022 highlighted the risks associated with the integration of cryptocurrency exchanges with traditional financial institutions. DOJ press release on FTX fraud details the charges and the extent of the alleged misuse of funds.
PHASE 4: M (No further instructions provided, assuming completion)
