Unmasking the Devastating ‘Damn’ Mining Malware: A Deep Dive into the V2EX Outbreak
- I recently fell victim to a mining virus attack, which prompted me to investigate and gather information to prevent similar incidents in the future.
- My goal in sharing this information is to raise awareness and potentially prevent others from falling prey to similar attacks.
- The first configuration appears to be a large-scale operation, with over 100 mining machines and more being added. Some machines are offline, but the total number is estimated...
Exposing Mining Virus Attackers: A Cautionary Tale
I recently fell victim to a mining virus attack, which prompted me to investigate and gather information to prevent similar incidents in the future. After a week of online research, I discovered two suspicious users who had compromised the c3pool.
My goal in sharing this information is to raise awareness and potentially prevent others from falling prey to similar attacks. I’ve uncovered two configurations that suggest malicious activity, which I’ll outline below.
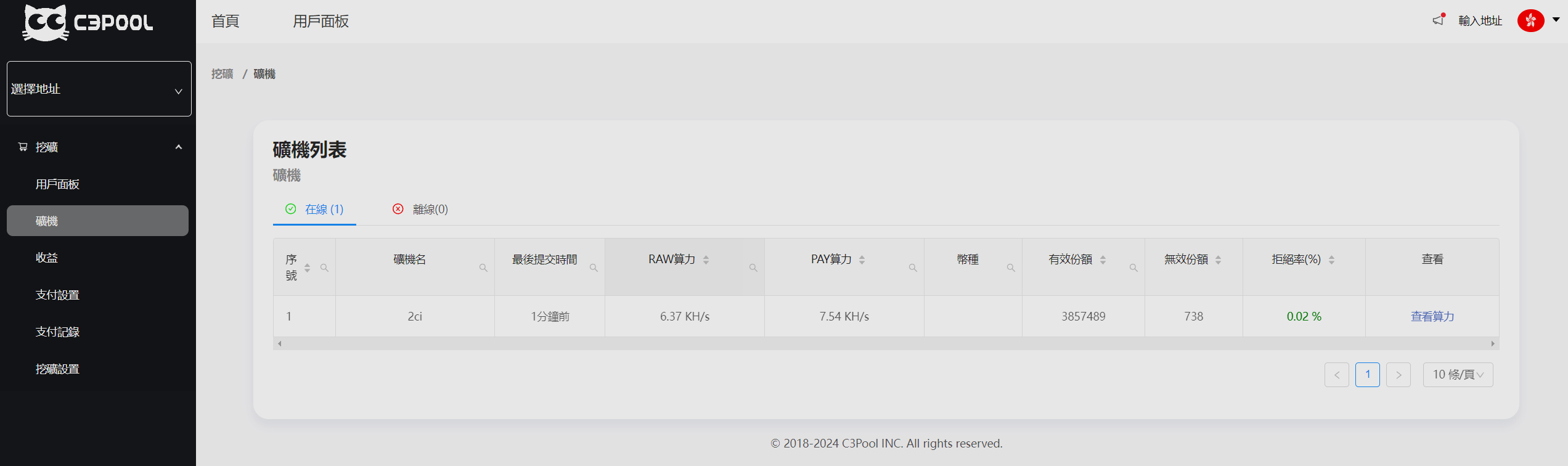
The first configuration appears to be a large-scale operation, with over 100 mining machines and more being added. Some machines are offline, but the total number is estimated to be around 120. Interestingly, some mining machines are named after IP addresses, suggesting a possible connection to a larger network.
The second configuration is smaller in scale, with only one mining machine detected. However, this could be a test run or a precursor to a larger operation.
Below are the wallet addresses associated with these suspicious activities:
45PX6QS4EhgRC1YbPNPRz8GmhyF7N4WVxQssZnhhc7xodKNNrQiEqxz9uQEMD6e8isjHVHt3Vk9Nqh5HMRgjVw4RC61FY5W

This configuration is associated with approximately 120 mining machines.
43LnXHx4St2VXP3EgCpH4UDu5LbsajdmLQHboSkdcEhFMcbiHxgVEstjHYjsVEZc7BMVqMoZRB1d79E3LQYuAqBWFPPvSdz


