
Wazuh Blue Team Playbooks: Proactive Cyber Defense
Blue Teams rely on playbooks to defend IT infrastructure. Discover how Wazuh Blue Team playbooks provide structured processes crucial for incident identification, containment, and remediation against cyber threats. Learn how these playbooks cover critical use cases like brute-force attacks, malware, and insider threats, ensuring consistent and timely responses.The article details the integration of Wazuh with security tools–offering enhanced incident response capabilities through automation. Stay informed on the essential elements of effective playbooks for proactive cyber defense, including prerequisites, workflows, and inquiry steps. News Directory 3 keeps you informed.Discover what’s next in proactive cyber strategies.
Wazuh Blue Team Playbooks for Incident Response
Updated June 09, 2025
Blue Teams are vital in cybersecurity, tasked with safeguarding an organization’s IT infrastructure—networks, endpoints, applications, and data—from diverse threats. Their responsibilities extend to ensuring continuous operations, monitoring for malicious activities, and providing real-time incident response. To function effectively, these teams rely on structured processes known as playbooks.
A Blue Team playbook offers a detailed guide on how to identify,contain,and remediate specific security incidents. These playbooks ensure incident responses are consistent, timely, and aligned with organizational policies and regulatory requirements, thereby minimizing the impact of cyberattacks. Thay include prerequisites,workflows,checklists,and investigation steps tailored for various incident scenarios.
Key Elements of Blue Team Playbooks
While organizations customize their playbooks to fit their unique environments, certain procedures are essential for effective incident response:
- Prerequisites: Foundational requirements that must be in place before launching an investigation, including security tools, defined roles, detection rules, and alerting logic.
- Workflow: The logical sequence of steps followed during incident response, typically involving detection, escalation, triage, containment, and resolution.
- Checklist: A task list to track and verify each step in the workflow, ensuring all necessary actions are taken to mitigate and remediate an incident.
- Investigation Playcards: Detailed, step-by-step instructions tailored to specific incident use cases and attack vectors, including log sources, indicators of compromise (IoC), MITRE ATT&CK techniques, containment, and recovery activities.
Incident Response (IR) is at the core of these playbooks, formalizing the process of detecting, investigating, and mitigating security incidents. Playbooks implement IR by translating high-level procedures into actionable steps for specific threats, making them essential tools for effective security operations.
Incident Use Cases Covered
Blue Team playbooks address various threat attacks, including:
- Brute-force login attempts across SSH, RDP, or web portals.
- Malware infections and unauthorized file changes.
- Insider threats and anomalous user behaviors.
- Privilege escalation and suspicious process executions on endpoints.
Wazuh Playbooks in Action
Wazuh offers several playbooks to enhance incident response capabilities. Here are a few examples:
Playbook 1: Credential Harvesting
Credential harvesting involves attackers attempting to steal login credentials to gain unauthorized access. Wazuh can detect this by monitoring system logs for suspicious activity.For example, PowerShell can be used to dump credentials, and Wazuh rules can identify such behavior.
Playbook 2: Web shell Detection
Web shells are malicious scripts uploaded to web servers, allowing attackers to execute commands remotely. Wazuh can inspect modified files for suspicious PHP functions often used in web shells, such as eval, exec, and base64_decode. When matched,Wazuh triggers a high-severity alert.
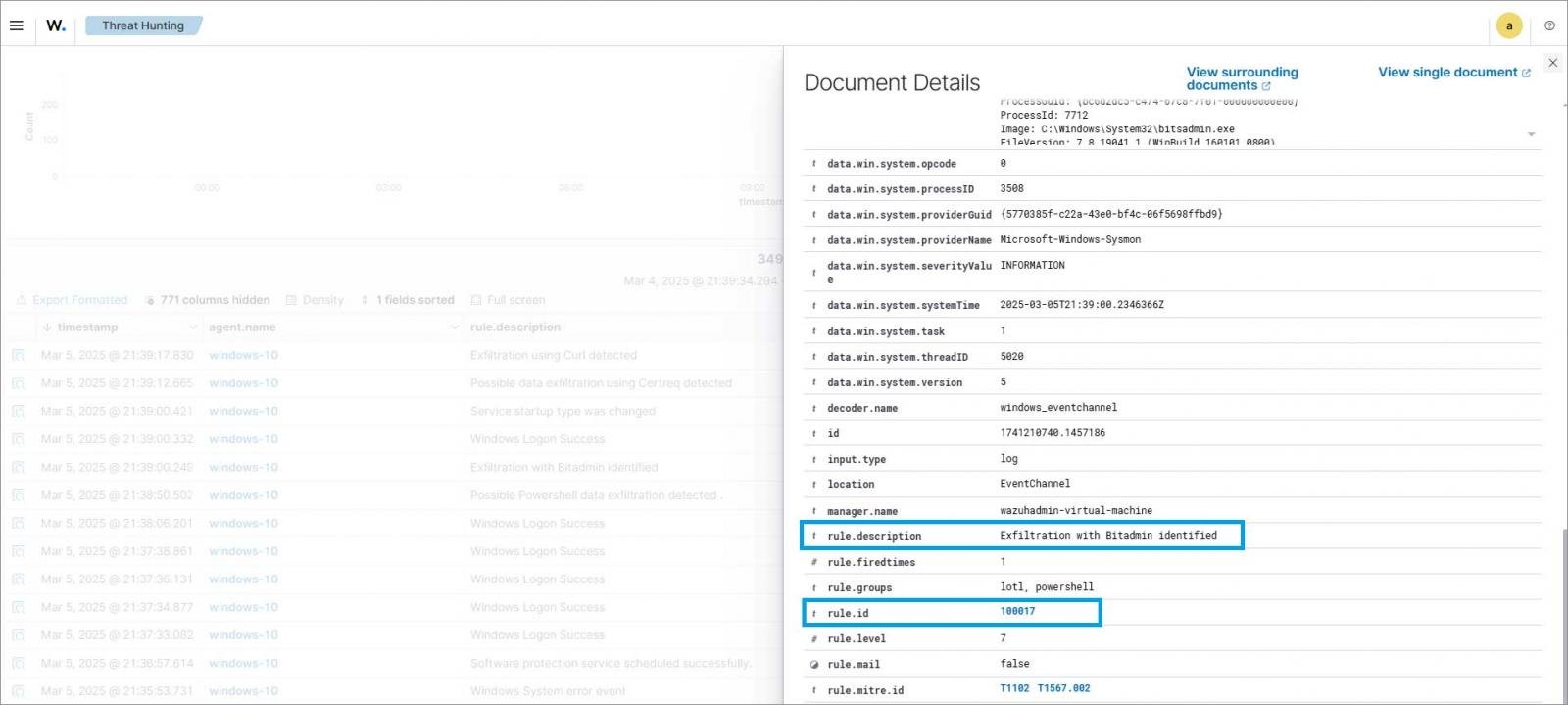
playbook 3: Suspicious Data Exfiltration
Data exfiltration can be difficult to detect, especially when attackers use legitimate tools, a technique known as Living Off the land (LOTL). Wazuh supports network activity monitoring, command execution tracking, and file access auditing to uncover abnormal outbound activity. By monitoring shell history, large file transfers, or tools like scp, curl, or netcat, Wazuh alerts teams to high-volume transfers or unusual destinations. Wazuh also uses GeoIP to flag connections from and to suspicious locations.
Playbook 4: Brute-Force login Attack
Brute-forcing is a common attack vector used to gain unauthorized access to endpoints and services. Wazuh detects brute-force attacks by correlating multiple authentication failure events across monitored endpoints. On linux endpoints, it identifies these attacks by parsing authentication logs such as /var/log/auth.log.
Wazuh decoders parse raw log data from authentication services to extract structured information about failed login attempts, including source IP address, username, and timestamp. Correlation rules analyze this data to detect patterns of rapid or repeated failures from the same IP address, triggering alerts for potential brute-force attacks. When the alert threshold is met, Wazuh uses its Active Response capabilities to run scripts to take action, such as blocking the offending IP address using firewall rules like iptables.

Integrating Wazuh with Othre Security Tools
To build effective Blue Team playbooks, organizations need tools that not only detect threats but also work seamlessly within a broader security ecosystem. Wazuh integrates with a range of external tools across the incident response lifecycle:
- SOAR platforms such as TheHive and Shuffle help automate case management and streamline the execution of incident response playbooks.
- Threat intelligence feeds including VirusTotal, AlienVault OTX, and AbuseIPDB, enrich alert data with external context, enabling faster and more informed triage.
- Ticketing systems like Jira integrate with Wazuh to facilitate efficient incident tracking,assignment,and team communication.
- Cloud platforms such as AWS, Azure, and GCP can be monitored by Wazuh to detect configuration issues, anomalous activity, and potential security breaches in cloud workloads.
What’s next
Wazuh’s adaptability supports various blue Team operations, providing tools to act quickly against threats, backed by community-driven threat detection rules and open-source integrations.
